The goal of this service is to provide your company with the ability to see the weak spots in your organization’s network that are vulnerable to threats.

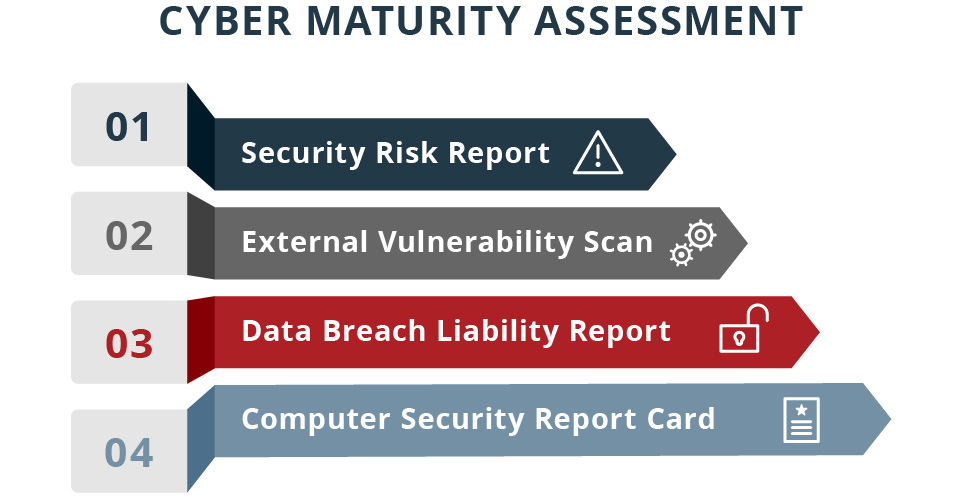
This service includes:
A security risk report – an overall showing a summary of risk score and problem areas in your network.
An external vulnerability scan – A comprehensive report include security holes and warnings of your network and firewall’s vulnerabilities.
Data Breach Liability report - To mitigate the risk of civil litigation and other penalties when a data loss or theft occurs, our cyber liability and data breach report is designed to expose just how vulnerable your organization may be.
Computer security report card – which assesses individual computers at a high level based on various security criteria. The report card provides a measure as to how well a computer complies with security best practices.
Identify gaps in your cybersecurity program across people, processes, and technology.
Determine the maturity of your organization and provides strong guidance on how to improve your security.
Compares the maturity level to other organizations facing similar risks and challenges across the board.
Specifically points out areas where you can improve your organization’s security level and points out the priorities on how to improve